Green Eagle Restore Protector Software Introduction
Green Eagle Kernel Protector Free is a comprehensive software that integrates virus and Trojan cleaning immunity, password account protection, hacker IE defense, and system repair and optimization.
Green Eagle Restore Protector software features
Can kill future Trojans
Real-time protection of various account passwords to ensure user security
Prevent malicious website modifications and arbitrary script viruses, and repair the system. Enhance system security and optimize system configuration
Internet cafes can set access passwords, support network batch processing startup, Internet cafe management channel mode calls, and LAN remote killing
Strengthened detection and killing of robot dog viruses and any variants!
How to use Green Eagle Restore Protector
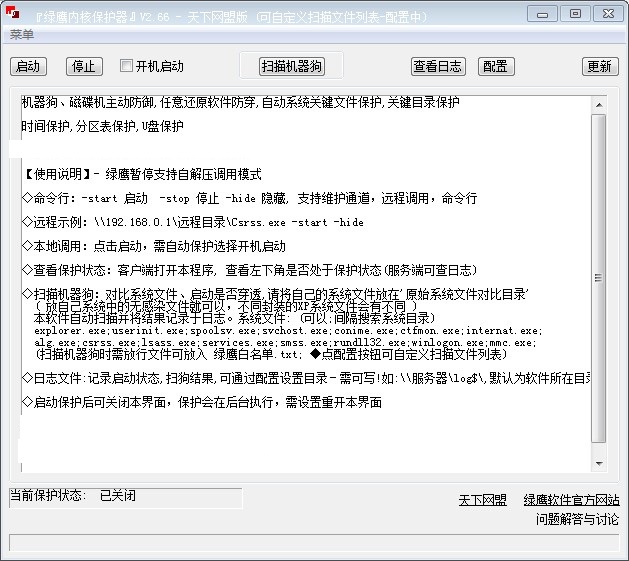
Green Eagle suspends support for self-extracting calling mode
Command line: -start to start -stop to stop -hide to hide, supports maintenance channel, remote calling, command line
Remote example: 192.168.0.1 remote directory Csrss.exe -start -hide
Local call: click to start, automatic protection is required and select boot to start
Check the protection status: Open this program on the client and check whether the lower left corner is in the protection status (the server can check the log)
Scanning robot dog: compare system files and see if startup is penetrated. Please put your system files in the 'original system file comparison directory'
(Just put the non-infected files in your own system, the XP system files in different packages will be different)
This software automatically scans and records the results in a log.
System files: (Yes; search system directories at intervals)
explorer.exe;userinit.exe;spoolsv.exe;svchost.exe;conime.exe;ctfmon.exe;internat.exe;alg.exe;csrss.exe;lsass.exe;services.exe;smss.exe;rundll32.exe;winlogon.exe;mmc.exe;
(Files that need to be released when scanning the robot dog can be placed in Green Eagle Whitelist.txt; click the configuration button to customize the scanned file list)
Log file: records startup status and dog scanning results. The directory can be set through configuration - it must be writable! For example: server log$, which defaults to the directory where the software is located.
You can close this interface after starting the protection. The protection will be executed in the background. You need to set up to reopen this interface.
Green Eagle Restore Protector Update Log
Working day and night just so you can be happier
are all gone!
Huajun editor recommends:
The editor of Huajun Software Park has compiled and collected software that you may like, such as:Kaspersky Total Security,360 safe,Blank And Secure,firewall app blocker,USB disk encryptorYou can download it from this site.






































Useful
Useful
Useful