Wireshark It is a great open source for Unix and WindowsnetworkProtocol Analyzer. It can detect network communication data in real time and also detect the network it captures.CommunicationData snapshot file. This data can be browsed through a graphical interface and network communications can be vieweddataDetailed content for each layer in the package. Wireshark is free to download.This version of wireshark is Chinese version. After the installation is completed according to the prompts, it will be the Chinese version.

Wireshark Chinese version usage tips
Wireshark font settings:
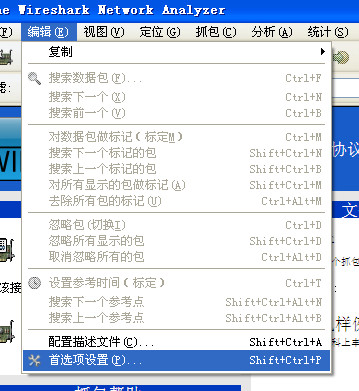
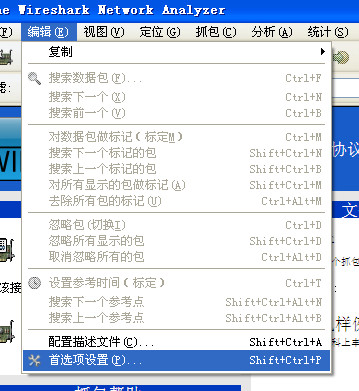
Note: If you choose Chinese, please choose the appropriate onefont, specifically set in Edit->Preference Settings->User Interface->Font!
Wireshark language settings:
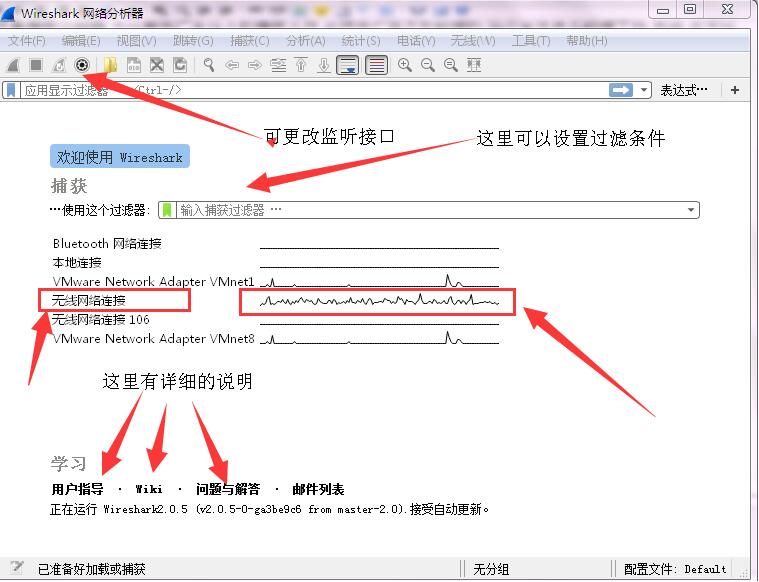
1. First, double-click the software to open it and enter the main interface. If there is no software on the desktop, you can find it in the software’s installation folder!
2. After opening the software, the value is shown in the figure below. The displayed interface is all in English.
3. Please use the mouse to click on the edit tab above and find the preferences button at the bottom!

4. In this way, we can enter the setting interface of the software. After opening it, as shown in the picture below, we can see that the language displayed at this time is English!
5. Click on the language column to change it to the chinese option!

6. If your computer system is the Chinese version, you can set it to the "use system setting" column!
7. After the setting is successful, click OK to save. At this time, you can see that the language of the interface has changed to the Chinese version!
Wireshark Chinese version packet capture tutorial
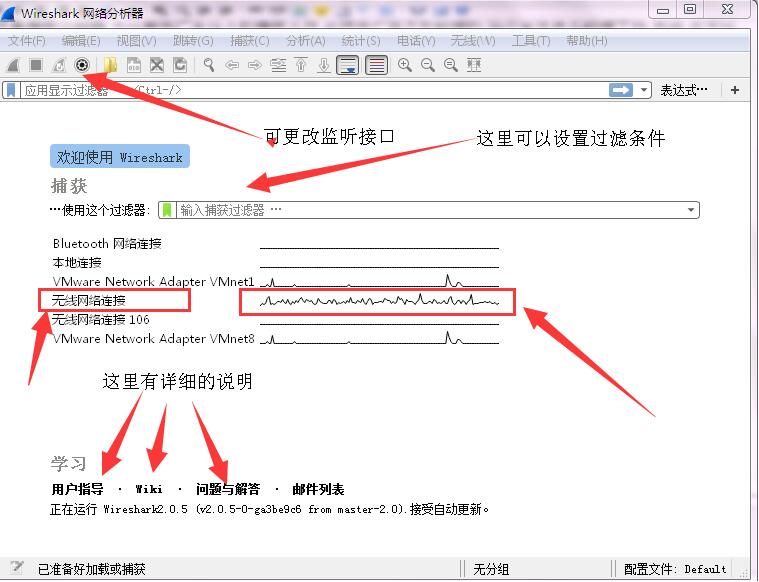
1. Set up the capture interface
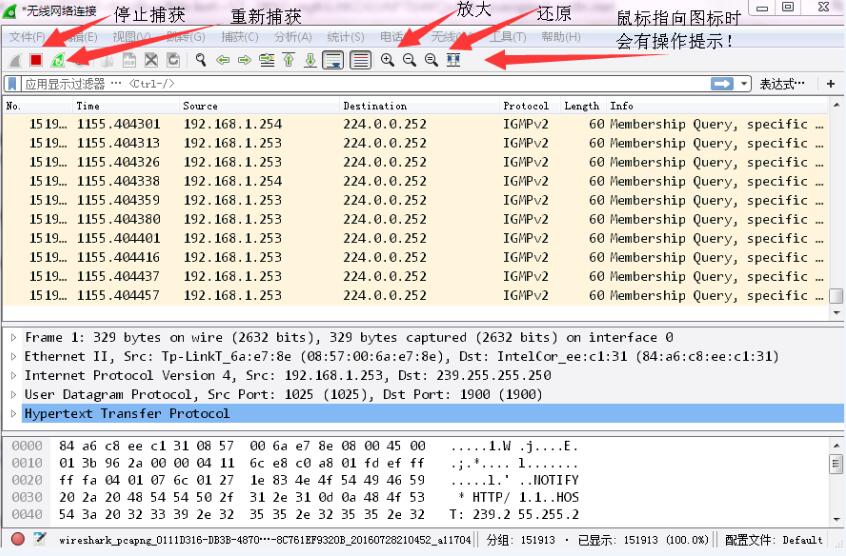
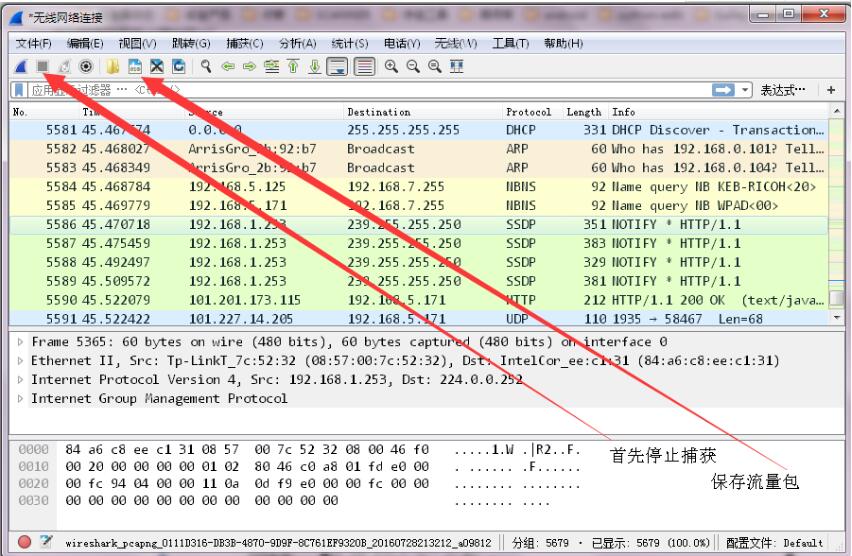
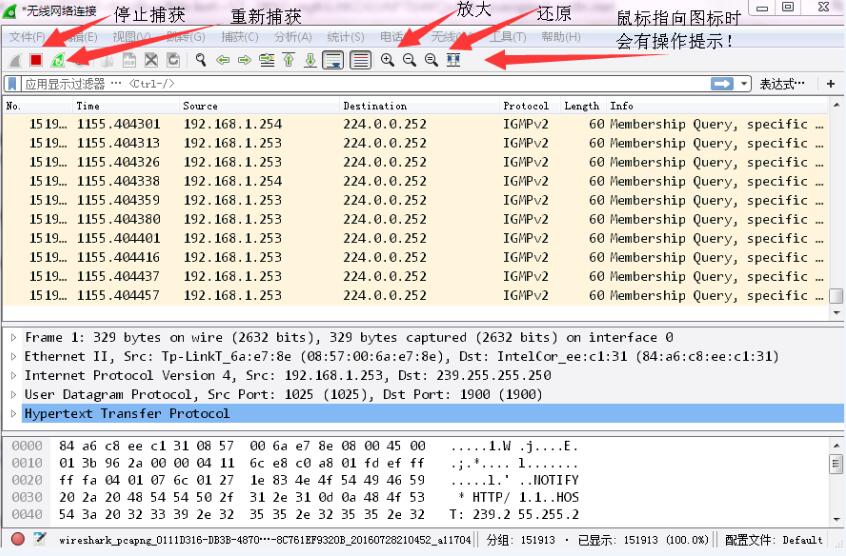
2. Stop and re-monitor
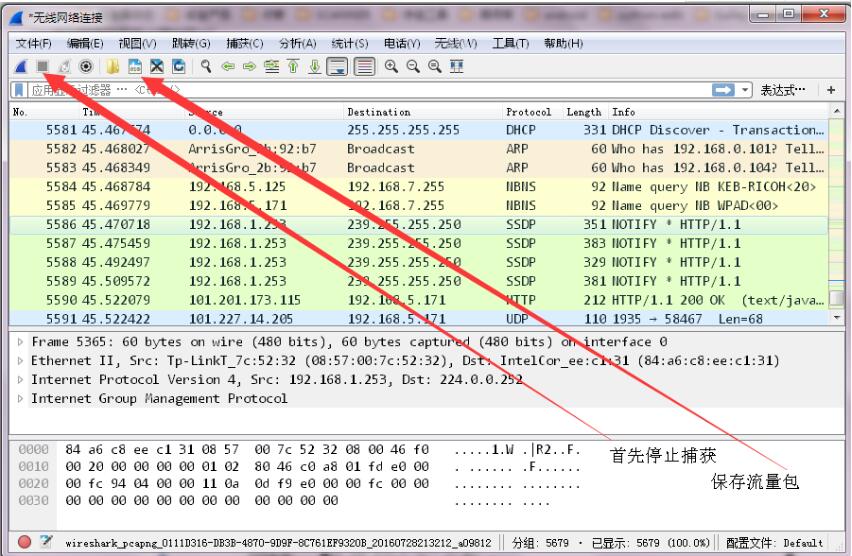
3. Saving of Wireshark data packets
After completing the capture of data packets, we may not be in a hurry to do analysis immediately, or the analysis we can do currently is not complete enough and needs to be deepened later... In this way, we need to save these data packets in files. There are also three ways to save data packets:
1 Use the Ctrl+S key combination;
2 Menu bar: Click "File"-->"Save" in sequence
3 Buttons of the main toolbar
WireShark is mainly divided into these interfaces:
1. Display Filter (display filter), used for filtering
2. Packet List Pane (packet list), displays the captured packets, source address, destination address, and port number. Different colors represent
3. Packet Details Pane (packet details), displays the fields in the packet
4. Dissector Pane (hexadecimal data)
5. Miscellanous(address bar, miscellaneous)
Wireshark Chinese version functions
Real-time network packet capture
Multi-interface support: Capture all network traffic from wired, wireless, VPN, virtual interfaces (e.g. Docker, VMware) and more.
Promiscuous mode: Capture the traffic of other devices on a shared network (requires permission).
Remote packet capture: Analyze remote host traffic through SSH or RPCAP protocols.
In-depth protocol analysis
Protocol coverage: Supports more than 3,000 protocols, including:
Link layer: Ethernet, IEEE 802.11 (Wi-Fi), PPP, VLAN.
Network layer: IP, IPv6, ICMP, ARP, RIP, OSPF.
Transport layer: TCP, UDP, SCTP, QUIC.
Application layer: HTTP/1.1/2/3, DNS, DHCP, SSL/TLS, MQTT, SMB, FTP.
Custom protocols: Parse private protocols (such as IoT device communication) through Lua script extensions.
Advanced filtering and searching
Display filter: Filter packets in real time based on protocol fields (such as http.request.method == "GET"), IP address, port number, etc.
Capture filter: Set conditions (such as tcp port 443) before capturing packets to reduce irrelevant traffic.
Search function: supports full-text search, hexadecimal value search, regular expression matching (such as finding sensitive information password).
Traffic statistics and analysis
IO graph: Draw trend charts such as packet rate, byte count, error rate, etc. in real time.
Protocol layered statistics: classified statistics based on protocol type, traffic size, session duration and other dimensions.
Geographical distribution of traffic (requires GeoIP database): Visually displays the source and destination of data packets (such as attack source IP map).
Session analysis: Rebuild TCP/UDP sessions and view the complete request-response process (such as HTTP interactions).
Packet export and replay
Format support: Export to PCAP, CSV, JSON, XML and other formats for easy integration with other tools (such as Python, Excel, ELK).
Replay attack simulation: Replay captured traffic through tshark or tcpreplay tools to test system security.
Detailed explanation of WireShark Chinese version filtering rules
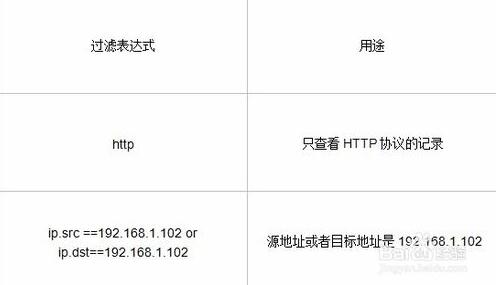
WiresharkfilterThere are two types of devices:
One is the display filter, which is the one on the main interface, used to find the required records among the captured records
One is a capture filter, which is used to filter captured packets to avoid capturing too many records. Set in Capture -> Capture Filters
save filter
In the Filter column, after filling in the Filter expression, click the Save button and give it a name. For example, "Filter 102",
There is a "Filter 102" button on the Filter bar.
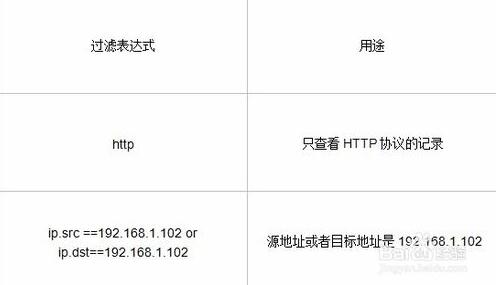
WiresharkRules for filtering expressions
Expression rules
1. Protocol filtering
For example, TCP only displays the TCP protocol.
2. IP filtering
For example, ip.src ==192.168.1.102 displays the source address as 192.168.1.102.
ip.dst==192.168.1.102, the target address is 192.168.1.102
3. Port filtering
tcp.port ==80, port is 80
tcp.srcport == 80, only displays the desired port of the TCP protocol is 80.
4. Http mode filtering
http.request.method=="GET", only displays the HTTP GET method.
5. The logical operator is AND/OR
WiresharkCommonly used filter expressions
Frequently asked questions about Wireshark Chinese version
1. What devices can be used with Wireshark to capture packets?
Answer: Wireshark can read live data from Ethernet, Token Ring, FDDI, Serial (PPP and SLIP) (if the OS it's running allows Wireshark to do so), 802.11 Wireless LAN (if the OS it's running allows Wireshark to do this), ATM connections (if the OS it's running allows Wireshark to do this), and "any" device that recent versions of libpcap support on Linux.
2. Why does sprint_realloc_objid not defined appear when I try to run Wireshark?
Answer: Wireshark can only be linked with UCD SNMP version 4.2.2 or higher. Your version of Wireshark dynamically links with this version of UCD SNMP; however, you have an older version of UCD SNMP installed, which means that when you run Wireshark, it tries to link to the older version, and fails. You must replace this version of UCD SNMP with version 4.2.2 or higher.
3. How does wireshark annotate data packets?
1. Open the wireshark software application on your computer.
2. Among the data packets captured by wireshark, right-click the selected data packet.
3. A drop-down menu will pop up, select "packet comment" in the menu

4. A window interface for packet comment will pop up. Enter the content that needs to be commented in the input box.
5. You can select the annotation by displaying a green color in the lower box. This displays the content of the comment.
4. How to print wireshark data packets?
1. In the list of data packages, select a data package, and then click the "file" option in the menu.
2. A drop-down menu will pop up, select the "print" option.
3. A print option will pop up. To print only one packet, check selected packet only.

4. Then select the name for printing to print the contents of the data packet.
5. Since this only demonstrates printing to a file on the computer, take the name of the computer.
6. Then find the file in the path on your computer, open the data package, and view the contents of the data package.
Wireshark Chinese version software features
The Wireshark packet capture tool has many powerful features:
Includes a rich display filter language and the ability to view TCP session reconstruction streams;
It supports hundreds of protocols and media types:
There is a command line version called tethereal similar to tcpdump (a network protocol analysis tool under Linux).
In the past, network packet analysis software was very expensive or specialized for commercial applications.
The emergence of Ethereal changed everything.
Under the protection of the GNU GPL General License, users can obtain software and its code for free, and have the right to modify and customize its source code. Ethereal is one of the most widely used network packet analysis software in the world.
Purpose of use of Wireshark Chinese version
1. Network administrators use Wireshark to detect network problems
2. Network security engineers use Wireshark to check information security-related issues
3. Developers use Wireshark to debug new communication protocols
4. Ordinary users use Wireshark to learn related knowledge of network protocols
Wireshark Chinese version workflow
(1) Determine the location of Wireshark. Without a correct location, it will take a long time to capture some data that is irrelevant to you after starting Wireshark.
(2) Select the capture interface. Generally, the interface connected to the Internet network is selected so that network-related data can be captured. Otherwise, the other data captured will not be of any help to you.
(3) Use capture filters. By setting capture filters, you can avoid generating capture files that are too large. In this way, users will not be interfered by other data when analyzing data. Moreover, it can also save users a lot of time.
(4) Use display filters. Usually the data filtered using capture filters is often still very complex. In order to make the filtered data packets more detailed, use the display filter to filter at this time.
(5) Use coloring rules. Usually the data filtered using the display filter are useful data packets. If you want to highlight a session more prominently, you can use coloring rules to highlight it.
(6) Construct a chart. If the user wants to more clearly see the changes in data in a network, the data distribution can be easily displayed in the form of charts.
(7) Reorganize data. Wireshark's reassembly function can reassemble information from different packets in a session, or reassemble a complete picture or file. Because transferred files tend to be large, the information is spread across multiple packets. In order to be able to view the entire picture or file, it is necessary to use the method of reorganizing the data.
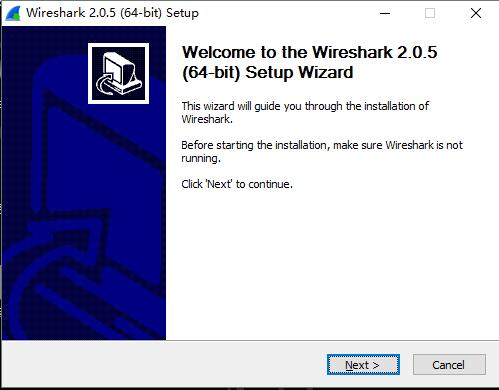
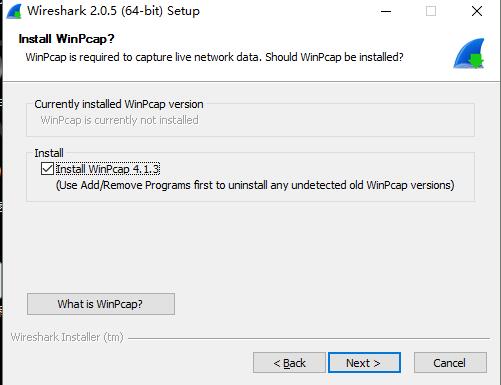
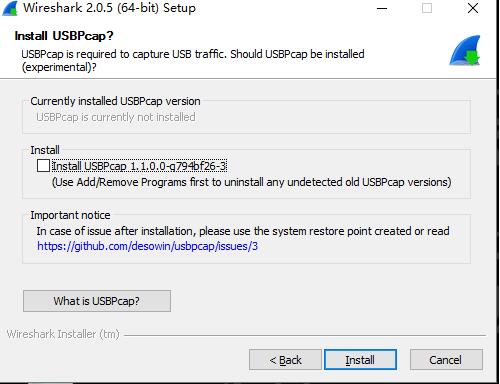
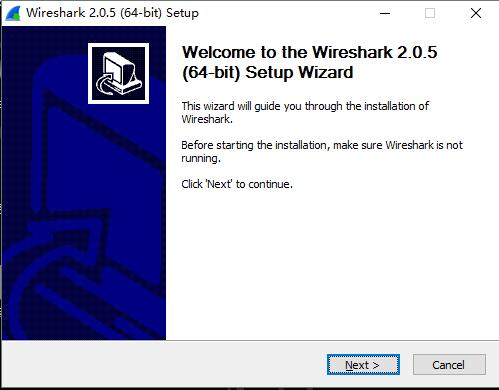
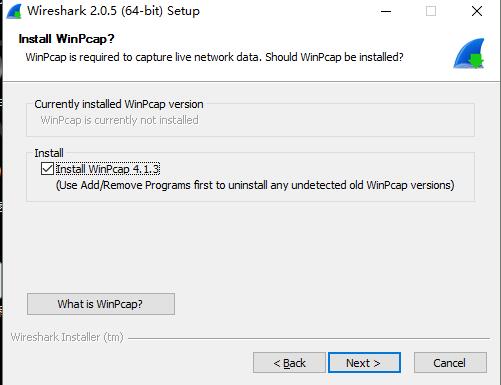
Wireshark Chinese version installation steps
1. Download the new version of wireshark installation package from this site, double-click to run it, and open the Wireshark installation wizard, as shown in the figure below:
2. Read the software agreement, agree to the agreement, and click the I Agree button:

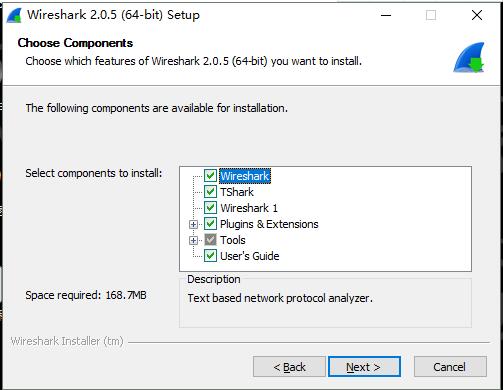
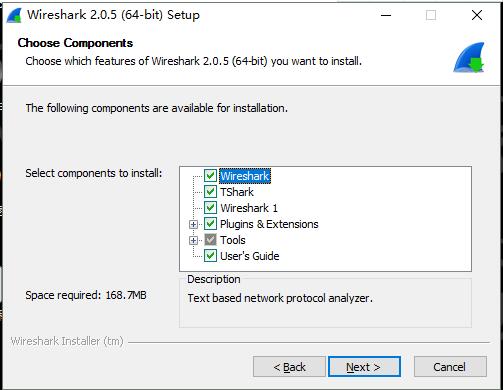
3. Select the installation component, it is checked by default, click Next:
4. Select additional tasks, which are checked by default, as shown in the figure below, click Next:

5. Follow the prompts and click Next until you reach the following interface. You can click [browse] to define the installation location of the software. It is installed on the C drive by default. The editor recommends that you click the Browse button to customize the installation path:

6. Prepare to install, click Next:
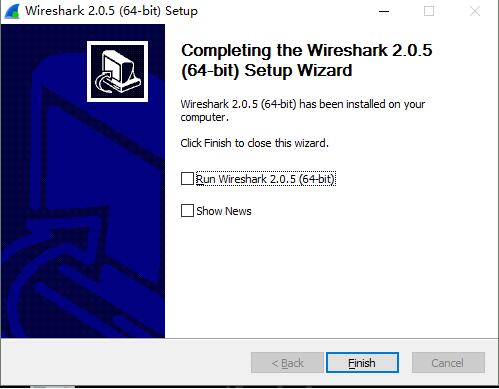
7. Click install to start the installation. The software installation may take a few minutes, please wait patiently.
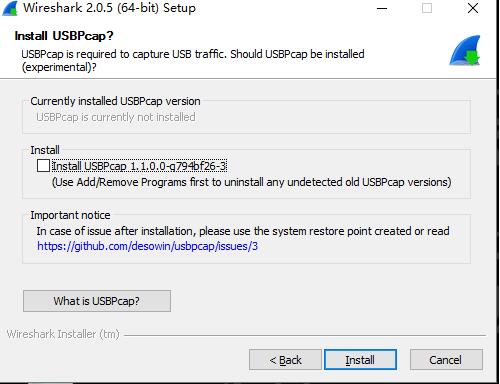
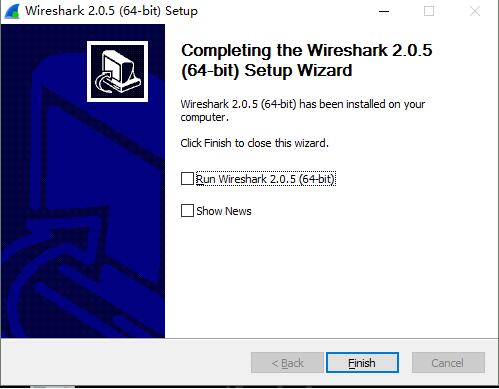
8. There will be a prompt after the installation is completed. Click [finish] to use the software.
Which one is easier to use, wireshark or winpcap? What is the difference?
WinPcap is a set of tools for network packet capture. It can be used to parse network packets on 32-bit or 64-bit operating platforms. It includes core packet filtering, a bottom-level dynamic link library, a high-level system function library, and an application program interface that can be used to directly access packets.
WinpcapIt is a free and open software system. It is used for direct network programming under Windows systems.
Most network applications access the network through the widely used sockets. This method makes it easy to implement network data transmission, because the operating system is responsible for the underlying details (such as protocol stack, data flow assembly, etc.) and provides functional interfaces similar to file reading and writing.
But sometimes, the simple approach isn’t enough. Because some applications require an underlying environment to directly manipulate network communications. Therefore, a primitive method of accessing the network that does not require protocol stack support is needed.
Wireshark (formerly known as Ethereal) is a network packet analysis software. The function of network packet analysis software is to capture network packets and display more detailed network packet information as much as possible.
The function of network packet analysis software [1] can be imagined as the work of "an electrician using an electric meter to measure current, voltage, and resistance" - just transplant the scene to the network and replace the wires with network cables.
In the past, network packet analysis software was very expensive or specialized for commercial applications. The emergence of Ethereal changed everything. Under the protection of the GNUGPL general license, users can obtain software and its source code for free, and have the right to modify and customize its source code. Ethereal is one of the most widely used network packet analysis software in the world.
The editor summarizes: The functions of the two are different, and users can choose according to their actual needs. Welcome to Huajun Software Park to choose and download.
Wireshark Chinese version update log:
1. Sweep the bug out and carry it out to the end
2. The most stable version ever
Huajun editor recommends:
After seeing the introduction provided by the editor of Huajun Software Park above, are you ready to start? Then download Wireshark and use it quickly. Huajun Software Park also provides network traffic statistics tools, Firefox Enterprise Edition, .NET, etc. for you to download and use.